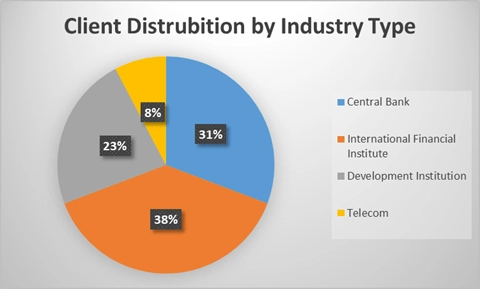
Who We’ve Assessed: A Snapshot of Our 2025 Client Landscape
Our 2025 assessments covered a diverse mix of financial institutions — including central banks, commercial banks, regional banks, microfinance institutions, International financial institutions and payment processors. Each client faces unique challenges in balancing compliance and operational efficiency, and our comparative data offers valuable insights into these varying risk postures.
The Data Speaks: Analysis from SWIFT CSP 2025 Findings
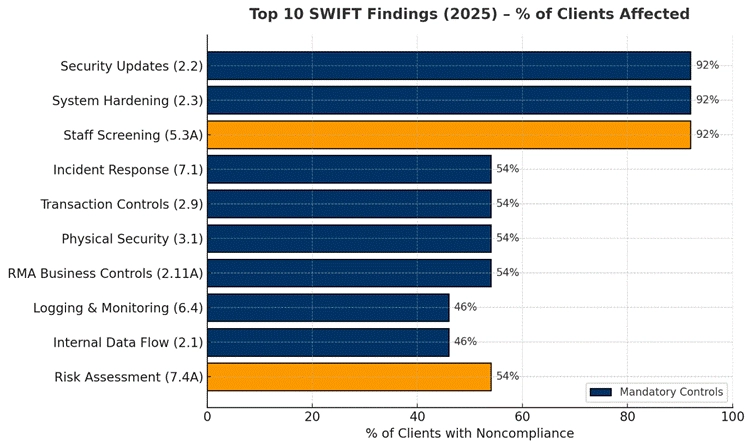
When we aggregate findings across clients, the data shows recurring weak spots in both technical and procedural controls.
The chart below highlights the Top 10 SWIFT Findings, ranked by total count and percentage of customers affected, offering a clear view of where institutions must pay attention.
Key Findings from WICS 2025 CSP Assessments
Our 2025 assessment cycle revealed that while control implementation across SWIFT environments continues to mature, several recurring weaknesses remain — particularly in areas requiring ongoing operational discipline rather than one-time compliance actions. When grouped by SWIFT’s seven security principles, Principle 2: Protect the Environment and Principle 5: Detect and Respond account for more than two-thirds of total noncompliance. This indicates that while governance and policy-level controls are largely in place, operational execution and evidence maturity remain the bottlenecks.
The most persistent weaknesses in 2025 were delayed security updates and inconsistent system hardening — both mandatory controls (2.2 and 2.3).
Even though most institutions maintain enterprise patch management programs, these often overlook SWIFT-specific components such as messaging interfaces, middleware servers, or jump hosts. Hardening checklists were frequently outdated or diverged from SWIFT and CIS benchmarks following system upgrades.
Risk: Unpatched or misconfigured systems remain one of the most direct routes for compromise, giving attackers footholds in critical SWIFT zones.
Despite technology investments, staff screening and role validation remain one of the most neglected areas. Advisory Control 5.3A was found deficient at nearly every institution assessed.
Screening was often limited to pre-employment checks, leaving out contractors, consultants, and periodic re-screening for financially sensitive roles. Periodic checks for precursor indicators such as criminal proceedings, conflict of interest and financial credit verification are often not conducted periodically to evaluate ongoing changes to insider threats.
Risk: Inadequate vetting increases the potential for insider fraud, collusion, or unauthorized access — risks that no firewall can mitigate.
Roughly half of the institutions lacked SWIFT-specific incident response playbooks, escalation matrices, or integration with enterprise SOC workflows.
While many organizations have a general IR plan, few have tested or simulated SWIFT payment fraud scenarios — a critical gap when rapid discovery & containment and fund recovery are time-sensitive.
Complementing this, logging and monitoring (Control 6.4) continues to lag, with limited 24×7 coverage and incomplete log collection from SWIFT secure zones.
Risk: Without a tested SWIFT response plan or targeted monitoring, organizations risk delayed detection and prolonged recovery in case of a breach by which time fraudulently transacted funds have moved out of jurisdiction and changed hands.
Controls governing transaction business hours, transaction limits, RMA relationships, and physical security remain inconsistent.
Many institutions still SWIFT and other payment systems open during off-hours or weekends without additional safeguards — a known vulnerability window exploited in prior SWIFT-related fraud cases.
Old/unused or dormant RMA counterparty relationships also persist which increase the likelihood of being abused by attackers. Many RMA records do not include message-type restrictions, increasing exposure to fraudulent or misdirected transfers.
Risk: Weak business controls and unmaintained counterparties create exploitable paths for fraudulent payment initiation or manipulation.
Roughly half of the organizations showed unclear internal back-office data flows between SWIFT interfaces and back-office systems. Encryption validation and configuration hardening were inconsistently implemented.
Risk: Attackers could intercept, alter, or monitor unencrypted message traffic within the secure zone, compromising transaction integrity.
Advisory Control 7.4A revealed that most risk assessments remain generic penetration tests, not realistic SWIFT simulations. Few organizations validate whether defensive controls activate during a SWIFT-targeted attack.
Risk: Without real-world testing, institutions underestimate risk exposure and fail to detect gaps in control effectiveness until after an incident.